Cellular World Congress (MWC) Barcelona is among the most demanding environments for community and safety operations. With 1000’s of attendees, unmanaged gadgets, and functions interacting in actual time, operational visibility and menace detection should operate flawlessly.
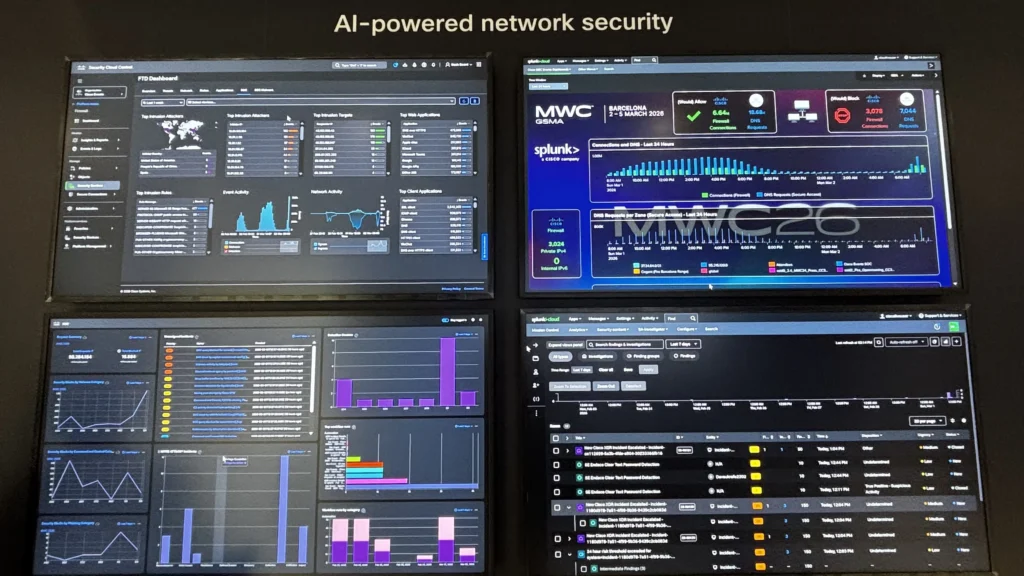
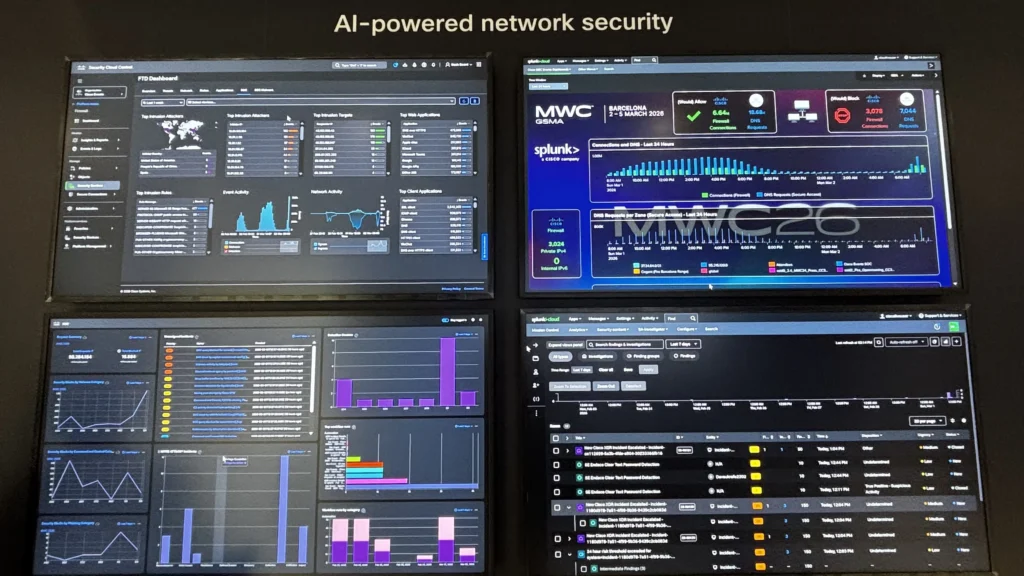
For the twond yr, the Cisco group leveraged Splunk, as well as to its different safety merchandise, to ship a unified Safety Operations Middle (SOC) and Community Operations Middle (NOC) expertise. Collectively, we used Splunk because the central information platform and integrating telemetry throughout a broad set of Cisco applied sciences.
What made this deployment significantly notable was not simply the breadth of integrations, however the pace and adaptability with which we operationalized the atmosphere.


The Structure: A Unified Operations Platform
On the core of the deployment was Splunk Cloud, performing as the only pane of glass for each SOC and NOC workflows.
We ingested information from a number of Cisco platforms, together with:


This structure allowed us to converge historically siloed operational domains right into a single analytics layer, enabling sooner correlation between community occasions and safety incidents.
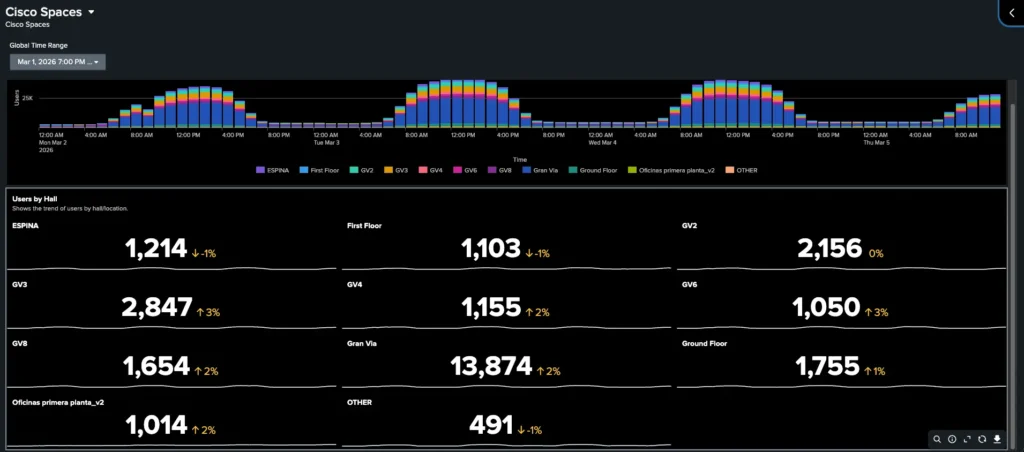
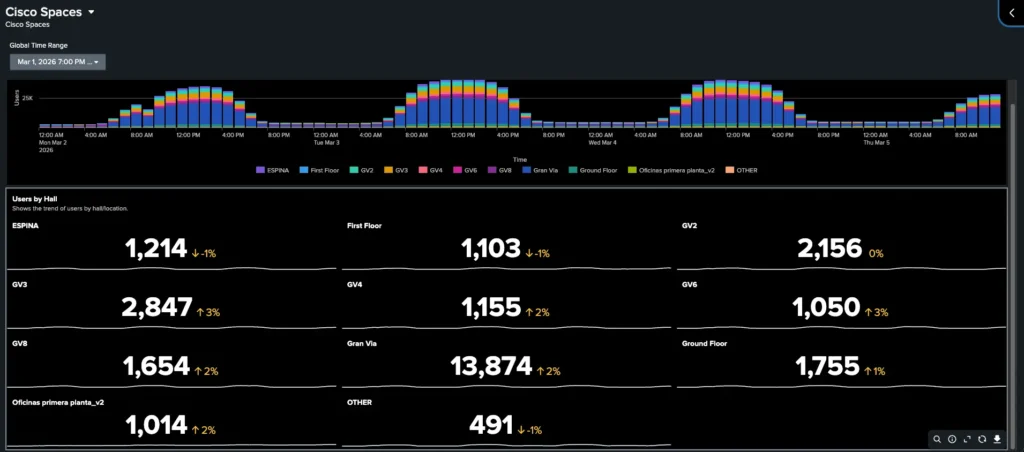
Constructing NOC Dashboards in an Afternoon
Probably the most impactful outcomes was how rapidly we have been in a position to ship operational visibility following numerous requests from different groups current on the occasion.
Utilizing Splunk’s information platform and visualization capabilities, we have been in a position to construct a totally purposeful NOC dashboard in just some hours. The dashboard supplied:
- Actual-time community utilization and availability
- Consumer connectivity metrics throughout wi-fi and wired environments
- Utility utilization indicators
As a result of all telemetry was collected inside Splunk, creating significant dashboards required minimal transformation work. This highlights a key benefit of utilizing a unified information platform: as soon as ingestion is solved, insights can comply with rapidly.
Bridging SOC and NOC: From Visibility to Context
Historically, SOC and NOC groups function in parallel, usually utilizing separate instruments and datasets. At MWC, we deliberately broke down that barrier.
By leveraging Splunk because the widespread platform:
- NOC occasions (e.g., latency spikes, utilization traits) could possibly be correlated with
- SOC indicators (e.g., anomalous visitors patterns, menace detections)
This convergence enabled sooner root trigger evaluation and diminished imply time to decision (MTTR), significantly in eventualities the place efficiency points or visitors anomalies had potential safety implications.
A First: Deploying the Cisco 6160 Firewall in a Public Occasion
A standout side of this deployment was the usage of the Cisco Safe Firewall 6160—marking its first deployment in a public occasion atmosphere.
Bringing this information into Splunk required a little bit of engineering:
Knowledge Pipeline Design
Due to the dimensions and efficiency traits of the firewall, we applied a structured ingestion pipeline:
- RSYSLOG Server
- Acted because the preliminary log aggregator supply for the firewall
- Dealt with high-throughput syslog ingestion from the 6160
- Offered buffering and normalization capabilities
- Saved information on the file system, offering one other layer of redundancy
- Splunk Heavy Forwarder (HF)
- Consumed logs from recordsdata produced by RSYSLOG
- Utilized parsing, filtering, and metadata enrichment
- Forwarded processed information securely to Splunk Cloud utilizing the S2S protocol
- Splunk Cloud
- Centralized indexing and analytics
- Enabled each SOC and NOC use circumstances
The next diagram illustrates the ingestion pipeline used to reliably transport high-volume firewall telemetry into Splunk Cloud:
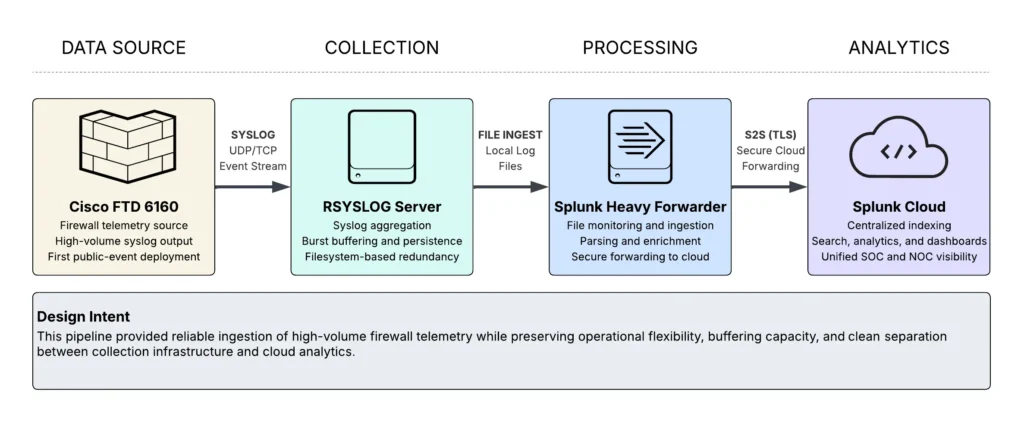
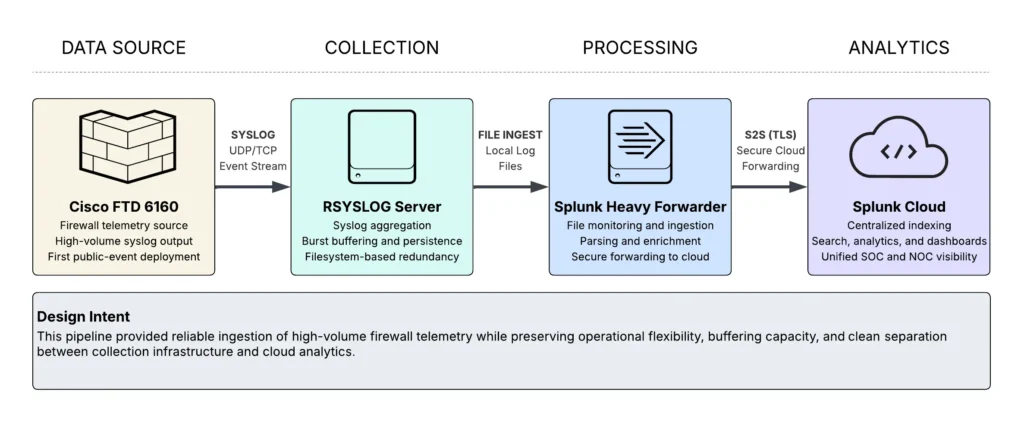
Why This Method Labored
- Scalability & Resiliency: RSYSLOG absorbed burst visitors with out dropping occasions and created an area copy of log recordsdata
- Flexibility: The Heavy Forwarder allowed us to regulate parsing/filtering earlier than ingestion, ought to we have to
- Cloud Integration: Clear separation between on-prem information assortment and cloud analytics
This pipeline ensured dependable ingestion of high-volume firewall telemetry whereas sustaining efficiency and information integrity.
Classes Discovered
A number of key takeaways from the deployment:
- Unification accelerates operations
Bringing SOC and NOC information right into a single platform improves operations and makes new insights doable
- Knowledge onboarding is the toughest—and most necessary—step
As soon as information is flowing and normalized, constructing dashboards and detections turns into considerably simpler.
- Edge engineering nonetheless issues in cloud-first architectures
Parts like RSYSLOG and Heavy Forwarders stay crucial for dealing with real-world information ingestion challenges.
- Pace is achievable with the fitting abstractions
Constructing a production-grade NOC dashboard in hours—not days—is life like when the platform is designed for it.
Take a look at the classes discovered from the Occasion SOCs we deploy world wide, with the white paper and newest blogs.
We’d love to listen to what you assume! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media

