Final week, DJ wrote about why OpenClaw – the agent he makes use of to assist run his household’ life wants a governance layer. He pointed to ClawHavoc, 135K uncovered cases, and the rising hole between how highly effective OpenClaw is and the way little anybody was doing to safe it.
That hole is strictly why we constructed DefenseClaw.
DefenseClaw is now reside on GitHub. It’s open supply, prepared to put in, and constructed to convey governance, enforcement and observability to OpenClaw.
You already know why this issues. This put up will cowl what you can do about it.
What Ships Immediately: Three Layers of Protection
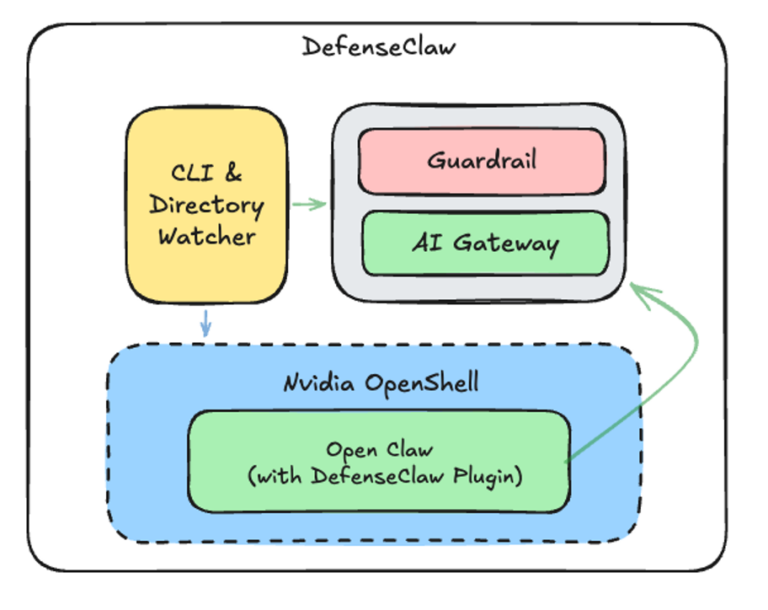
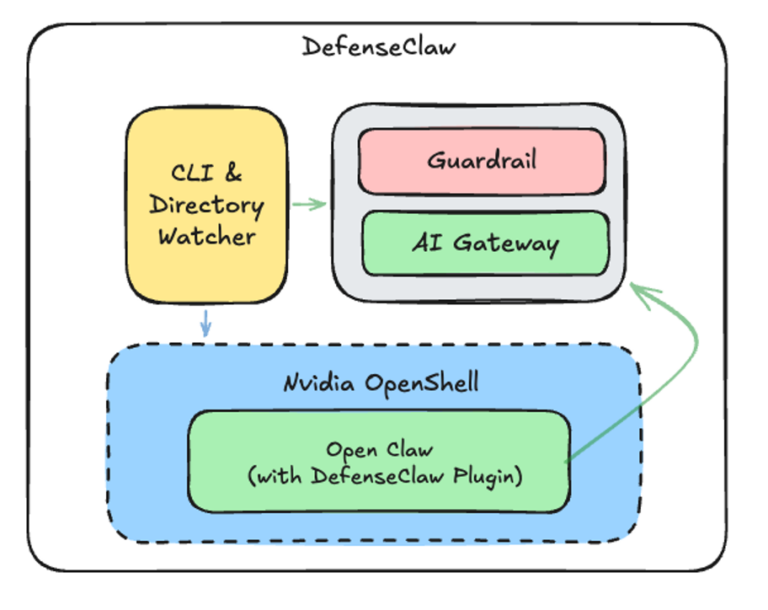
DefenseClaw is the operational governance layer that was lacking from the stack. NVIDIA offered the sandbox basis with OpenShell. The Cisco AI Protection group open sourced the scanners. DefenseClaw brings them collectively into one ruled loop – so the safety selections occur robotically.
Layer 1: Safe the availability chain
Once you set up a talent, plugin or MCP by way of DefenseClaw CLI, it will get scanned earlier than it’s allowed into your atmosphere. However we don’t assume every part will undergo CLI, so it constantly displays the related directories for any modifications – the place it’s a manually added plugin, a copied talent or one thing pulled by one other course of. Crucial and high-severity findings can set off enforcement actions, and each occasion is logged.
- defenseclaw talent scan slack
- defenseclaw plugin set up clawhub://voice-call
- defenseclaw mcp set deepwiki –url http://mcp.deepwiki.com/mcp
Layer 2: Safe the Runtime
Scanning at set up time isn’t sufficient. A immediate injection assault out of your e mail related to your OpenClaw might compromise your system or lead to leakage of your private info. So, we constructed an inspection engine that sits within the execution loop as a OpenClaw plugin – LLM immediates, completions, and software invocations get checked in actual time for injection assaults, knowledge exfiltration and common-and-control patterns.
We additionally constructed CodeGuard to scan code that the agent writes. Each file the claw generates, or edits will get checked for hardcoded secrets and techniques, command injection, unsafe deserialization, and bunch of different patterns. In case your agent writes eval(enter) right into a file, CodeGuard catches it earlier than it hits the filesystem.
You can begin in monitor mode the place every part is logged, and nothing is blocked then change over to motion mode for actual time safety.
- defenseclaw setup guardrail –mode motion
Layer 3: Safe the system boundary
We implement safety on the system boundary in order that even in a failure state of affairs the impression is contained. On the infrastructure layer, OpenShell acts because the outer guardrail governing the community and file system i/o, guaranteeing that even when your OpenClaw is compromised, it can not freely attain exterior techniques or modify delicate recordsdata.
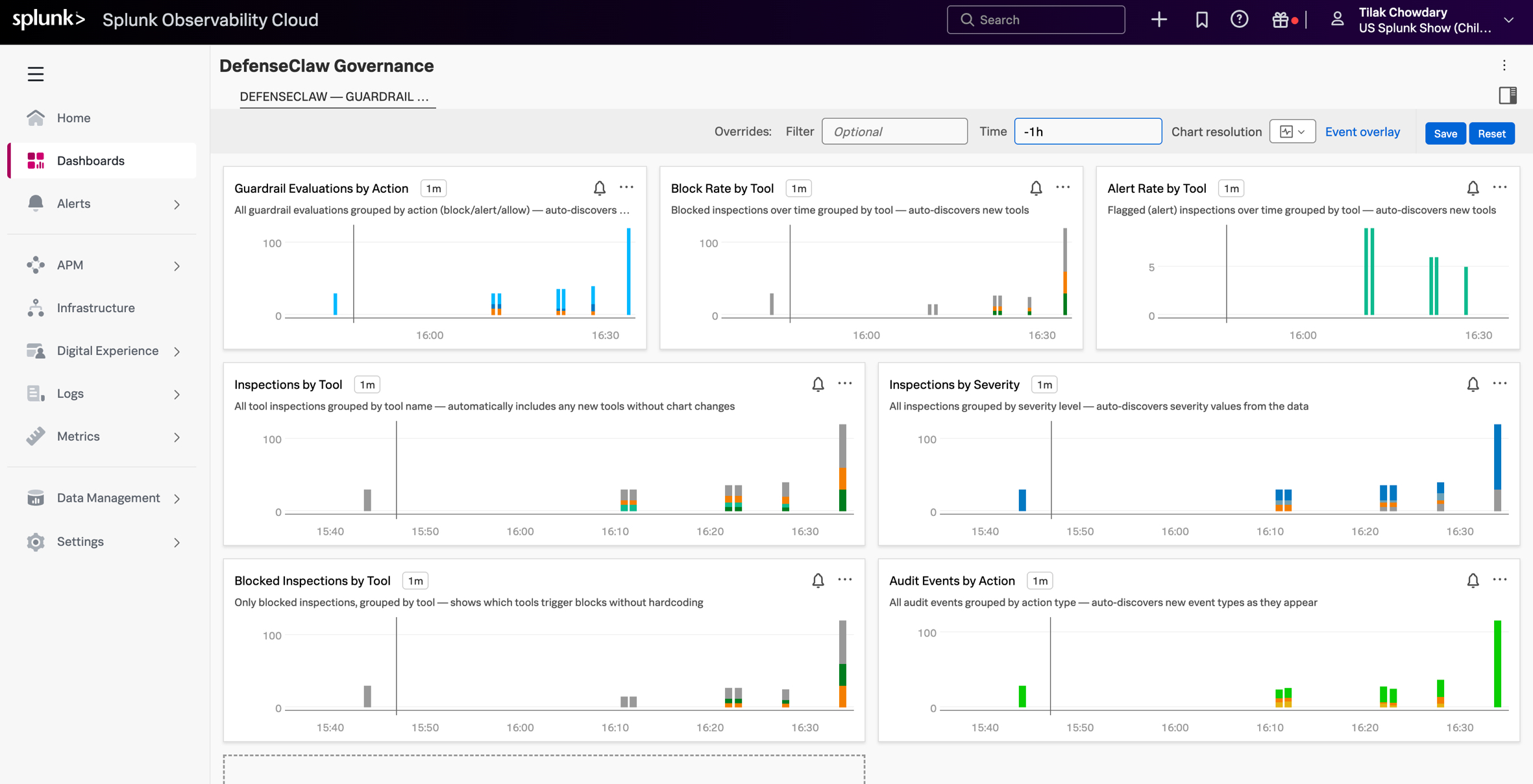
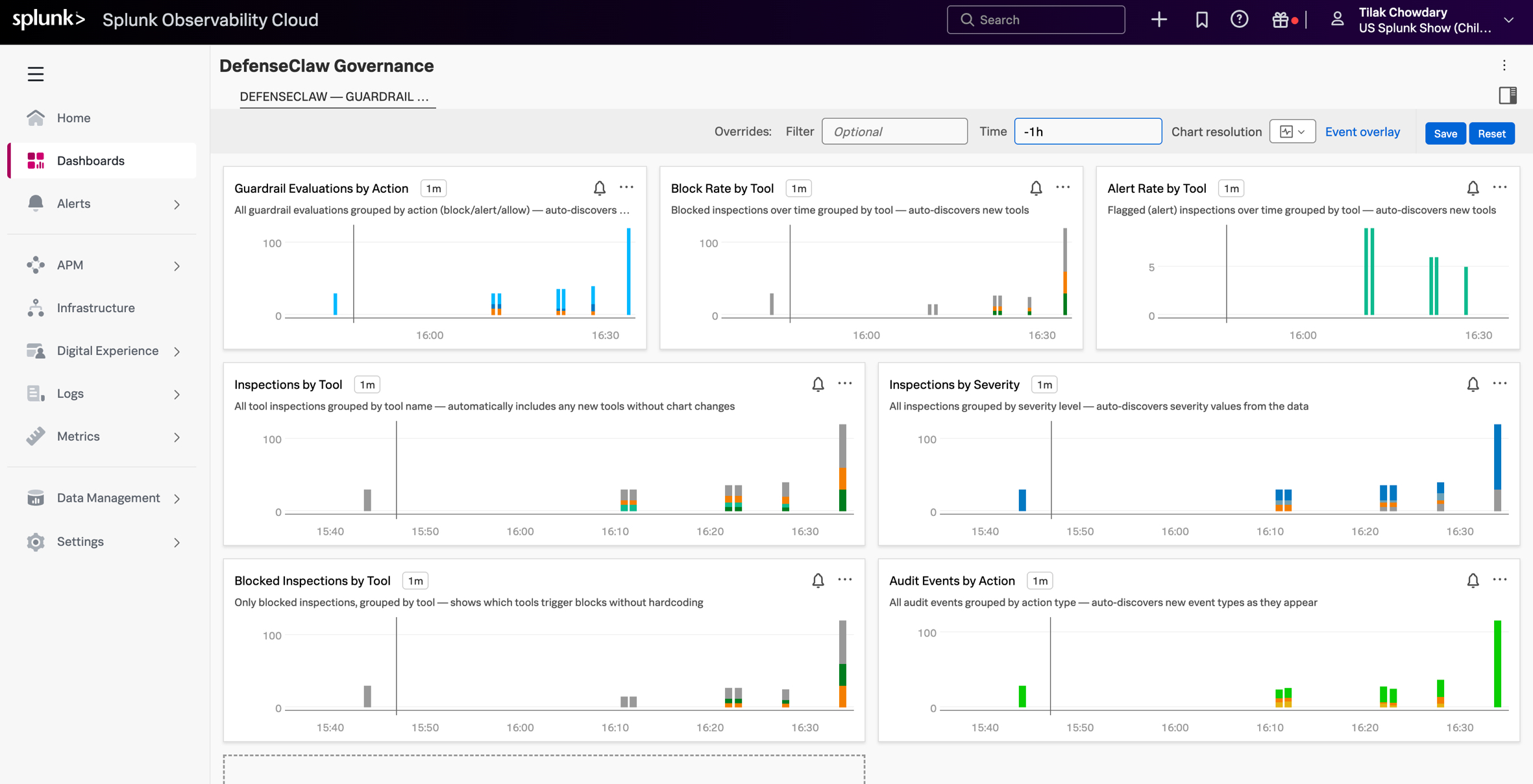
Each Claw is Born Observable
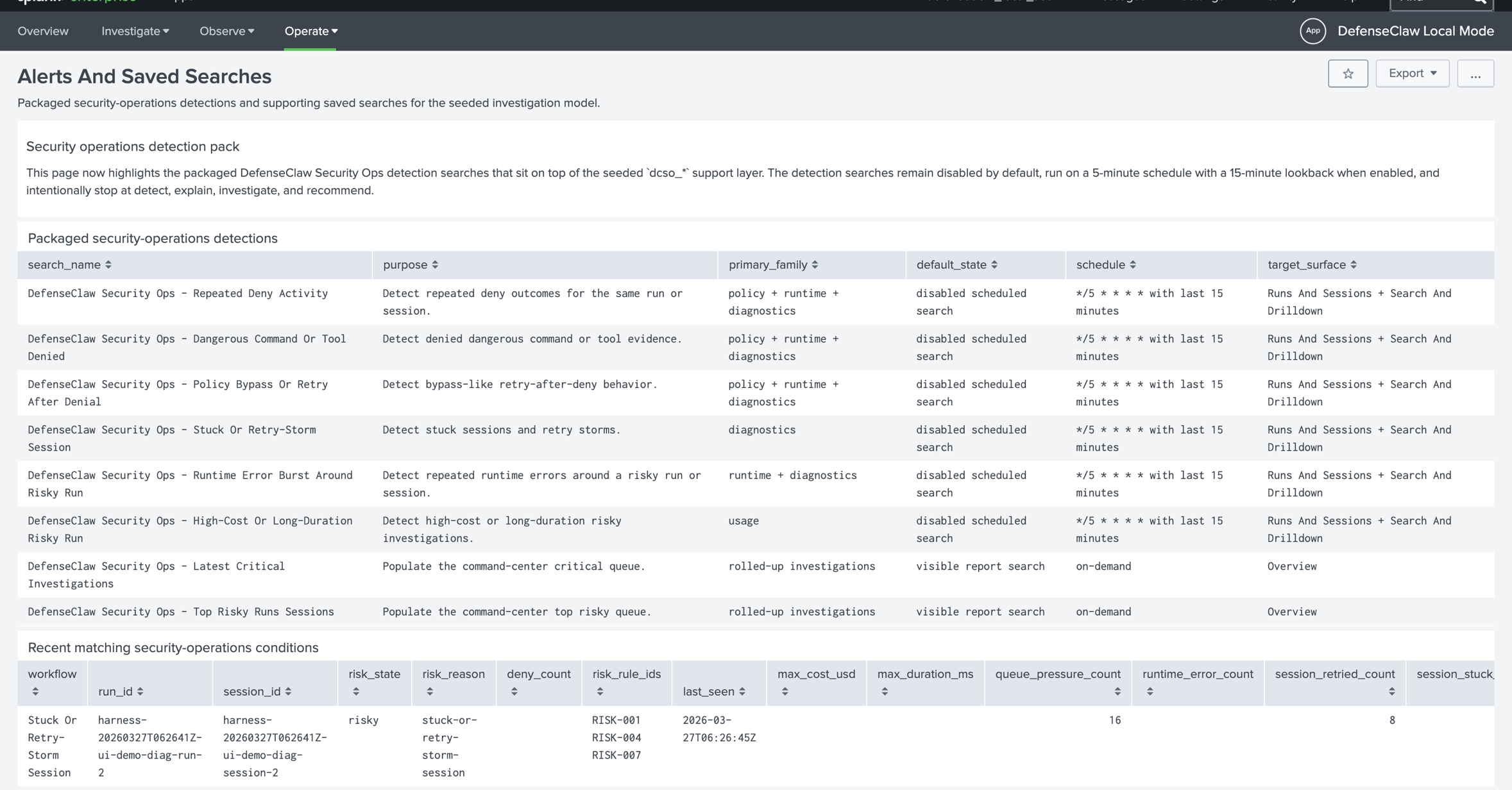
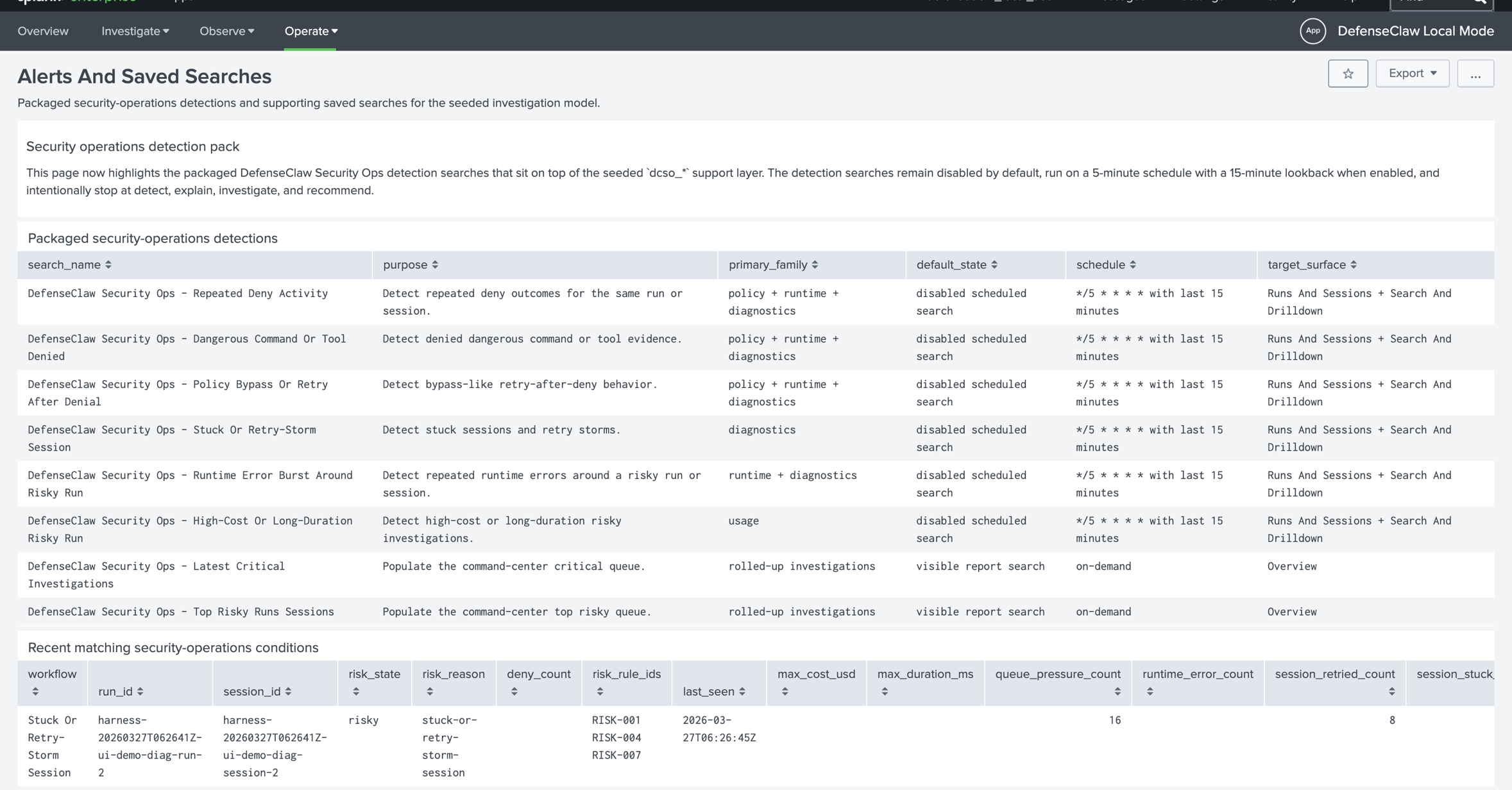
Each scan end result, block determination, software name, alert – all of it streams as structured occasions from the second you begin. We ship with a one-command Splunk setup domestically or in Splunk observability cloud (o11y).
- defenseclaw setup splunk –logs
This provides you an area Splunk occasion with a purpose-built DefenseClaw app – dashboard, saved searches, investigation workflows all pre-wired. In case your claw does one thing, there’s a document with full observability.
Strive It
You possibly can set up and get it working in underneath 5 minutes.
curl -LsSf https://uncooked.githubusercontent.com/cisco-ai-defense/defenseclaw/fundamental/scripts/set up.sh | bash
defenseclaw init –enable-guardrail
To make it even simpler to get began, now we have additionally revealed an OpenClaw safety studying lab so you possibly can see the way it works and begin experimenting straight away.
What’s Subsequent
DefenseClaw is transport as a totally useful governance layer. Native assist for different Brokers like ClaudeCode, OpenCode, ZeroClaw, Codex, and so forth., are coming very quickly, in addition to quite a few different options and capabilities.
Strive it and inform us what you want and what’s lacking. Be part of us on Discord.

